Your upgrade to macOS Monterey has been blocked for now.
Apple has recently released their newest operating system, macOS Monterey. LBNL IT does not recommend upgrading to macOS Monterey at this time. We would like to caution our users to be careful before deciding to upgrade.
You need to ask yourself the following questions before upgrading to macOS Monterey:
Is your computer hardware compatible?
Are all your peripheral devices compatible?
Is all your installed software compatible?
Do you have the installers and installation keys for that software, if you need to reinstall?
If you do upgrade, do you have a full backup of your computer?
If you do upgrade, make sure to backup your computer before upgrading/installing.
Feel free to reach out to IT if you have any questions. You can contact our support staff by:
Opening a chat session at go.lbl.gov/ITChat
Sending an email to [email protected]
Calling 510-486-4357
Attempting to log in with blank, default, and common usernames and passwords is a widely used attack technique. Unlike most enterprise or corporate networks, Berkeley Lab has an open computing environment so changing default credentials is especially important. To facilitate science and collaboration, most networks are open both to other computers at Berkeley Lab and to the global, public internet as a whole.
Background
Default passwords are standard, known userid/password pairs that are preinstalled into an operating system, database or software. This information is likely widely available in the system manual, online documentation, forums, and other sites. Default passwords are useful for installations, access management, support and programming purposes but, if left unsecured, still pose a serious security risk to all Berkeley Lab systems. An attacker can completely compromise a system that uses default passwords and then use it as a foothold to attack the rest of the laboratory. Consistent with Department of Energy and Office of Science requirements, Berkeley Lab manages risk to systems using a cost-effect approach that balances mission and risk. See RPM - Cyber Security Risk Management Approach.
All Laboratory employees and affiliates are responsible for the life cycle management of security, operations, backups, and maintenance of Laboratory information and IT that they use or manage. Review the RPM - Lifecycle Management for Information, Hardware, Software, and Services for more information.
Impacted Systems
Recently, the IT Division’s Cyber Security group uncovered several instances of default passwords in use on the Berkeley Lab network. Through routine scanning Cyber Security found default credentials in active use throughout the Lab RaspberryPi devices, personal network equipment, and with new software installations with services like Grafana and Nagios.
Each occurrence could result in a security issue for the Lab network. It is important to identify software and systems that are likely to use default passwords. Provided below are other examples of systems and devices which commonly use default passwords:
Routers, access points, switches, firewalls, and other network equipment
Software packages, including vendor demonstrations or customer support portals
Databases and management systems, including IDMS, Oracle, and Microsoft SQL
Web applications and administrative web interfaces
Embedded systems and devices, e.g. BIOS PC computer chips, Unix root user accounts, out-of-band management interfaces (IPMI, iDRAC, ILO, etc)
Industrial Control Systems (ICS) systems
Remote terminal interfaces like Telnet and SSH
Recommended Actions
Default passwords are easily exploited since information is readily available and so many systems are left unmonitored. Remain vigilant about keeping the Lab environment secure by taking the following steps:
Always Change Default Passwords. Change default passwords as soon as possible and absolutely before deploying the system on a network with internet access. Use a sufficiently strong and unique password. See Choosing and Protecting Passwords - Security Tip (ST04-002).
Use a Password Manager. Use a password manager to help with replacing default logins, creating strong passwords, and reminders to update or secure credentials. See IT FAQ on LastPass password manager or search software.lbl.gov.
Restrict Network Access. Restrict network access to trusted hosts and networks and only allow internet access to required network services. If remote access is required, use secure access methods such as VPN, or SSH. See Minimum Security Requirements.
Maintain Software and Firmware Updates. Turn on automatic updates for your programs and devices to ensure the latest security patches are applied. If automatic updating is not an option, set a calendar reminder to review updates and credentials in a timely manner. Review IT Best Practices.
For assistance with configuring secure systems and networks, contact the IT division by emailing [email protected] or submit a support request at help.lbl.gov.
In support of Cybersecurity Awareness Month, the IT Division is highlighting phone scams and offering tips on how to avoid attacks. Scammers often take advantage of busy times throughout the year when people are distracted or vulnerable, such as during holidays, tax season, back-to-school, and global events like coronavirus. Every year, Americans report billions of dollars in total losses to scam callers. In addition to practicing proactive defensive security measures, education and outreach remain an integral component to avoiding and preventing phone scams. Continue reading to learn more, view examples, and recommendations.
Key Data
The 2021 Truecaller report indicates a 22% increase over the past year in the number of Americans who lost funds due to phone scams and 59% who received scam calls related to COVID-19. Of those who lost money to phone scams, 60% were due to calls made using automated dialing technology, i.e. robocalls. About 3 in 5 Americans reported an overall increase in spam calls and/or text messages (see SMS phishing).
Illegal and unwanted calls comprise the largest source of consumer complaints according to a 2021 Federal Communications Commission (FCC) report. Voice service providers continue to make advancements in analytic call blocking and labeling tools to protect consumers. Companies report few false positives and no public safety issues.
A survey of local consumer data from the Federal Trade Commission (FTC) reveals the top 5 fraud categories in the San Francisco, Oakland, Berkeley metro area to be imposter scams, online shopping, internet services, prizes or sweepstakes, and telephone and mobile services.
Example 1:
In the examples below, a scammer uses local numbers and an automated message to contact you regarding a fake expired vehicle warranty. Auto warranty scams were the top unwanted call complaint filed with the FCC in 2020. If you accidentally answer a robocall or press a button in response to a recording, simply hang up immediately. Be sure to report the message as spam and block the number.
Example 2:
The examples below are provided by the FCC and focus on COVID-19 robocall scams. The audio transcripts both reference coronavirus and a critical and urgent need for your attention. These scammers prey on victims during emergencies and may offer free home testing kits, fake health insurance, vaccine appointments, loan repayment offers or other financial assistance.
Do not respond to calls from unknown numbers. The Department of Justice has a hotline for consumers who believe they have been a victim of a scam or fraud related to COVID-19. The National Center for Disaster Fraud Hotline is 1-866-720-5721.
Social Security Scam: Hello this is a call from the Social Security Administration. During these difficult times of the coronavirus, we regret to inform you that we have got an order to suspend your socials immediately within 24 hours due to suspicious and fraudulent activities found on your socials. We are contacting you as this case is critical and needs your urgent attention. To get more information about this case please call immediately on our department number 888-991-2325. I repeat 888-991-2325.
Listen to sample audio. (Source: Nomorobo)Diabetic Test Kit Scam: If you are diabetic and using insulin, we can qualify you to get a free diabetic monitor and a complimentary testing kit for coronavirus. To learn more, please press 1, otherwise please press 2.
Listen to sample audio. (Source: YouMail)
Example 3:
Tech support scams are a common scheme for criminals to gain remote access to your computer. They may call you and identify themselves as Microsoft or Apple employees and claim your computer is infected with a virus or has a technical problem only they can fix.
Tech Support Scam: In this example, an FTC investigator records a scammer who insists her computer is infected and guides her to purchasing antivirus software. Listen to an FTC undercover call with a tech support scammer.
Keep in mind that real tech companies will not contact you to let you know there’s a problem with your computer. Real computer security warnings will not instruct you to call a phone number or purchase a product. If you are concerned about your computer security, contact [email protected].
Tips for Recognizing Phone Scammers
Familiar entities: Scammers often impersonate representatives of a well-known organization, e.g., IRS, Medicare, Social Security, a utility or tech company, e.g. PG&E, Microsoft, and Apple, or even nonprofits and charitable groups.
Spoofed numbers: Scammers might use technology to spoof or mimic fake phone numbers appearing on your caller ID. The phone number may have a local area code or appear related to a government or work agency.
Critical Timeline: Scammers will indicate there is an urgent, time-sensitive problem you need to resolve or perhaps a prize or investment to claim quickly. The emphasis is on guiding you to act as fast as possible under threat or duress.
Payment Method: Scammers frequently demand specific methods for payment which are difficult to reverse, such as via money order, prepaid cards, gift cards, use of a money transfer company, a bank wire transfer, or depositing a fake check.
Recommended Actions to Stay Safe
Be aware of the attack methodology, remain vigilant, and report anything suspicious. Exercise caution with unexpected requests, offers, or phone calls not initiated by you. View the social engineering page for more tips on how to recognize scams.
Do not share your private login or financial information. If you are unsure, verify the request with the organization directly through the official website or phone number.
Do not grant access to your devices to an unknown caller unless you initiated the request and can verify they are a legitimate representative of your support group.
Ensure your equipment meets Berkeley Lab Minimum Security Requirements.
Stay up to date with required Cyber Security Training and Secure Your Computer.
Report any suspected or known breach of personal information to [email protected] as soon as possible. For other related questions, please email [email protected] to open a ticket.
How to Block and Report Spam Calls
Block the caller on your mobile and locate the option to label the call as spam.
Block phone numbers on iOS and Recognize and avoid phony support calls
Block a phone number on Android and Use caller ID & spam protection
Federal Communications Commission (FCC)
Federal Trade Commission (FTC)
Report a Scam to the FTC at ReportFraud.ftc.gov
Did you know that October is national Cybersecurity Awareness Month? The IT Division is releasing a series of educational tips and reminders to promote the importance of cybersecurity across Berkeley Lab. Be sure to also check out events and learning opportunities hosted by UC Berkeley and UCOP at https://security.berkeley.edu/cybersecurity-awareness-month-2021.
Recently, the IT Division Cyber Security team noticed an increase in phishing attacks via SMS text message. Attackers are able to avoid email filtering by phishing via SMS messages Phishing typically involves attempts to acquire or disclose personally identifiable information (PII) such as your username, password, and other sensitive information. The phishers would then steal your username and password to use on the real website or sell your information to other scammers. Real examples are provided below followed by recommended actions to take and instructions for reporting spam messages.
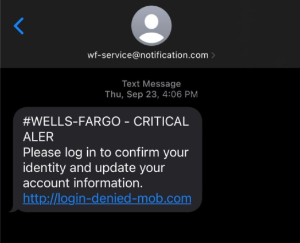
Example 1:
In this example, the attacker sends a text from a fake address mimicking the name of a financial institution and alerts the user to log in with personal account information.
Notice the domain of the sender and link do not match the institution’s official address. If you logged into this lnk, your bank credentials would be stolen. Legitimate companies will not ask for information about an account via SMS. Some links may point to a spoofed website which closely emulates the authentic version. Do not click the links. Contact the institution directly from their official website to verify the validity of messages.
Example 2:
In the following examples, the attacker sends an SMS message from an unknown number and asks the user to follow a link to schedule or confirm a change in a delivery.
Scammers craft these messages to trick you into clicking a malicious link which then sends you to a fake portal or may install harmful malware on your phone. Do not click the links and report such messages as spam.
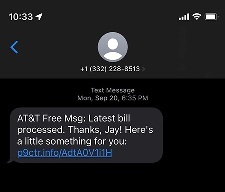
Example 3:
This example is similar to Example 2 but indicates the user receives a small gift for paying a bill.
Attackers may make claims of problems with an account or promises of free gifts. It is common for scammers to send fake messages asking a user to take some action before claiming a package or a prize. Be skeptical of unexpected opportunities which sound too good to be true. Do not trust requests to share or confirm personal information via text.
Recommended Actions
Take steps to ensure devices meet Minimum Security Requirements.
Follow IT guidance to help secure computers: Tips to Secure Your Computer.
Stay up to date with Cyber Security Training requirements.
The best defense for these attacks is to be aware of the attack methodology, remain vigilant, and report anything suspicious. See the social engineering page for more tips on how to avoid phishing and other scams.
Report any suspected or known breach of personal information to [email protected] as soon as possible. For other related questions, please email [email protected] to open a ticket.
How To Report Spam Text Messages
Report it on the messaging app you use. Look for the option to report junk or spam.
Copy the message and forward it to 7726 (SPAM).
Report it to the Federal Trade Commission at ReportFraud.ftc.gov.
Windows has recently released their newest operating system, Windows 11. LBNL IT does not recommend upgrading to Windows 11 at this time. We would like to caution our users to be careful before deciding to upgrade or install.
You need to ask yourself the following questions before choosing to upgrade:
Is your computer hardware compatible?
Are all your peripheral devices compatible?
Is all your installed software compatible?
Do you have the installers and installation keys for that software, if you need to reinstall?
If you do upgrade, make sure to backup your computer before upgrading/installing.
Feel free to reach out to IT if you have any questions. You can contact our support staff by:
Opening a chat session at go.lbl.gov/ITChat
Sending an email to [email protected]
Calling 510-486-4357