MFA Help Pages:
| Children Display | ||
|---|---|---|
|
| Info |
|---|
MFA is highly effective at preventing unauthorized access to your accounts. With MFA, an attacker will not be able access your account simply by stealing your password. The attacker must also steal your phone or Yubikey to access your account. Use of MFA is mandatory for all LBL staff and affiliates after 9 December 2019. |
What are my options to set up Multi-Factor Authentication?
- Self-Service Google Authenticator setup:
- The instructions to set up Google Authenticator on your own are here: Install Google Authenticator and Setup MFA
- If you need any assistance with the setup, you can contact the IT Help Desk at x4357
- Walk-in support with IT:
- Desktop Support is located at 46-125 between the hours of 8:00 AM and 5:00 PM. Yubikeys are $50 and you must provide a Project ID. There is no additional charge for Google Authenticator but you must bring your smartphone with you to 46-125.
- On-site support with IT:
- If on-site support is required, the hourly rate for technician work is $100/hour including travel time and ticket processing time. Yubikeys are an additional $50. You must provide a Project ID before a technician will be sent out. There is no additional charge for Google Authenticator but you must have your smartphone with you.
What exactly is Multi-Factor Authentication?
Single-factor authentication, such as typing a password, is increasingly an insufficient protection for online accounts. The combination of phishing, malware, and brute-force guessing presents a formidable threat to single-factor authentication. Unauthorized access to your account can have significant harm, both to you personally (financial harm for example) and to the mission and reputation of Berkeley Lab.
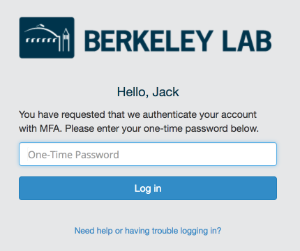
Multi-factor authentication (MFA) requires more than one factor to authenticate. Most commonly, MFA requires typing a password (first factor) and entering a one-time code (second factor) generated by Google Authenticator on your phone or a Yubikey plugged into your computer.
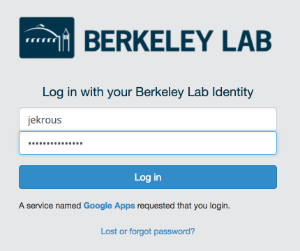
MFA at Berkeley Lab enables you to have a second factor protecting your Lab account. When you log into enterprise applications (behind the Shibboleth Single Sign-On), you will first be prompted for a username and password and then a one-time code.
If you have questions regarding MFA, please submit a help ticket or contact the IT Help Desk at 4357.
| Pop away |
|---|
What is multi-factor authentication?
Multi-factor authentication is the method where a user is granted access to a resource once they have provided several separate pieces of evidence proving who they are. For example, think about accessing your bank accounts via an ATM machine. To prove to the bank who you are and that you can have access to your bank account, you insert your ATM card (something you have) and enter your PIN number (something you know). You have provided the bank with two forms of authentication enabling the bank to give you access to your accounts.
Why use multi-factor authentication?
Plain and simple, to secure resources against unauthorized personnel and ensure only authorized users access appropriate resources.
Security Tokens at Berkeley Lab
A methodology to implement multi-factor authentication requires the use of one-time passwords (OTP) or what we call security tokens. OTP can be provided either by software or hardware solutions. Berkeley Lab IT has opted from both solutions. Software security tokens are generated from Google Authenticator and the issuance of hardware tokens with varying security privileges can be obtained from Berkeley Lab IT.
Multi-factor Authentication at Berkeley Lab
Berkeley Lab uses MFA on several systems, including:
- Windows login - requirement of multi-factor authentication for Operations personnel logging into Windows Active Directory computers (sometimes known as StrongID)
- HRIS (other than the website) - requirement of multi-factor authentication for HR personnel logging into Berkeley Lab HR databases
- Web-based single sign on (SSO) - requirement of multi-factor authentication for Shibboleth providing Lab personnel logging into Berkeley Lab resources like email, calendar, LETS, etc.
- Lawrencium HPC cluster - All HPCS Clusters require One Time Passwords (OTPs) for Authentication
How do I get started using Multi-factor Authentication?
The full process is outlined here. Please note that Berkeley Lab employees must submit a help ticket to obtain any hardware security OTP tokens.