|
|
||||||||||||||||||
...
Below are screenshots of the simulated phishing campaigns that have been run so far at LBNL.
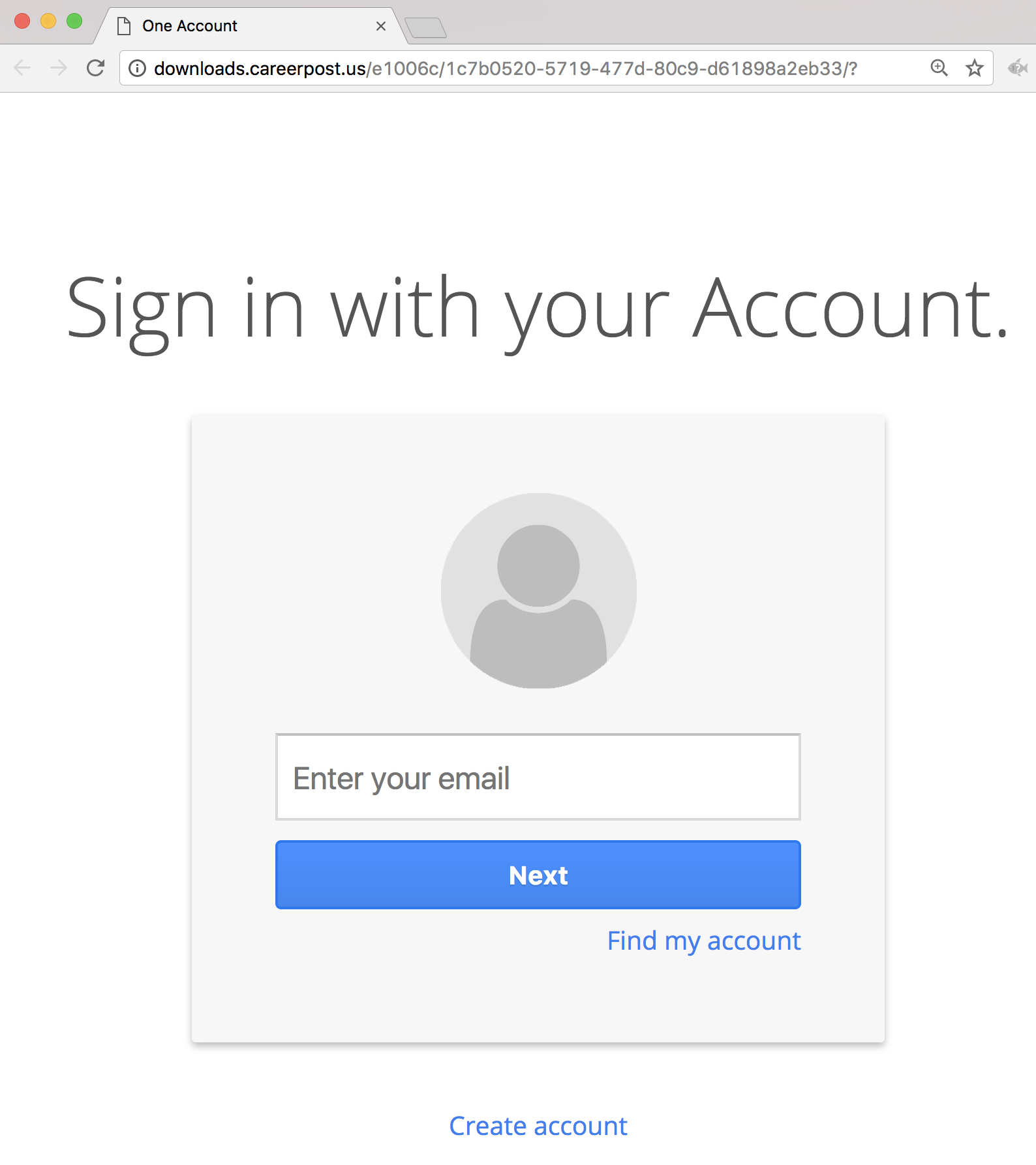
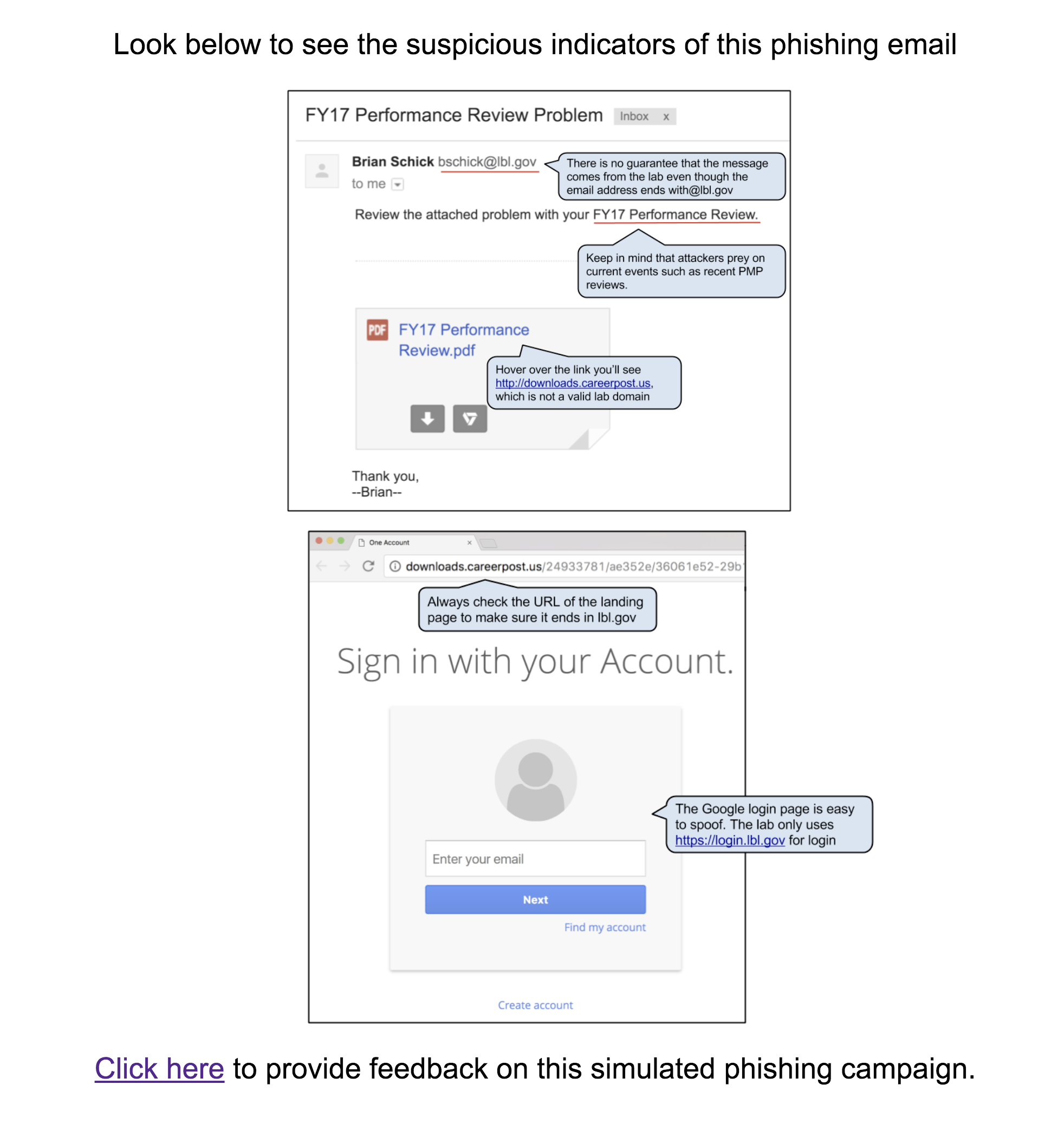
#5 2017-10-16: FY17 Performance Review Problem
This email was intended to get users to question the legitimacy of the pdf attachment even though the sender appears to have a “real” lbl.gov email address. The attachment link in the email directed to a spoofed google login page in order to retrieve the username and password of the user. The fake employee Brian Schick was created to demonstrate the situation where an email address is spoofed or compromised. Emails sent to Brian was answered by the security group.
...
The Landing Page:
The Education Page:
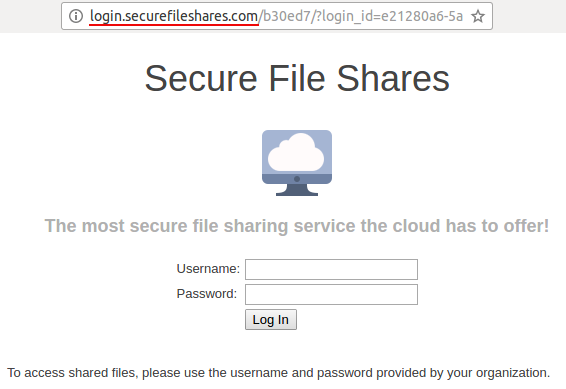
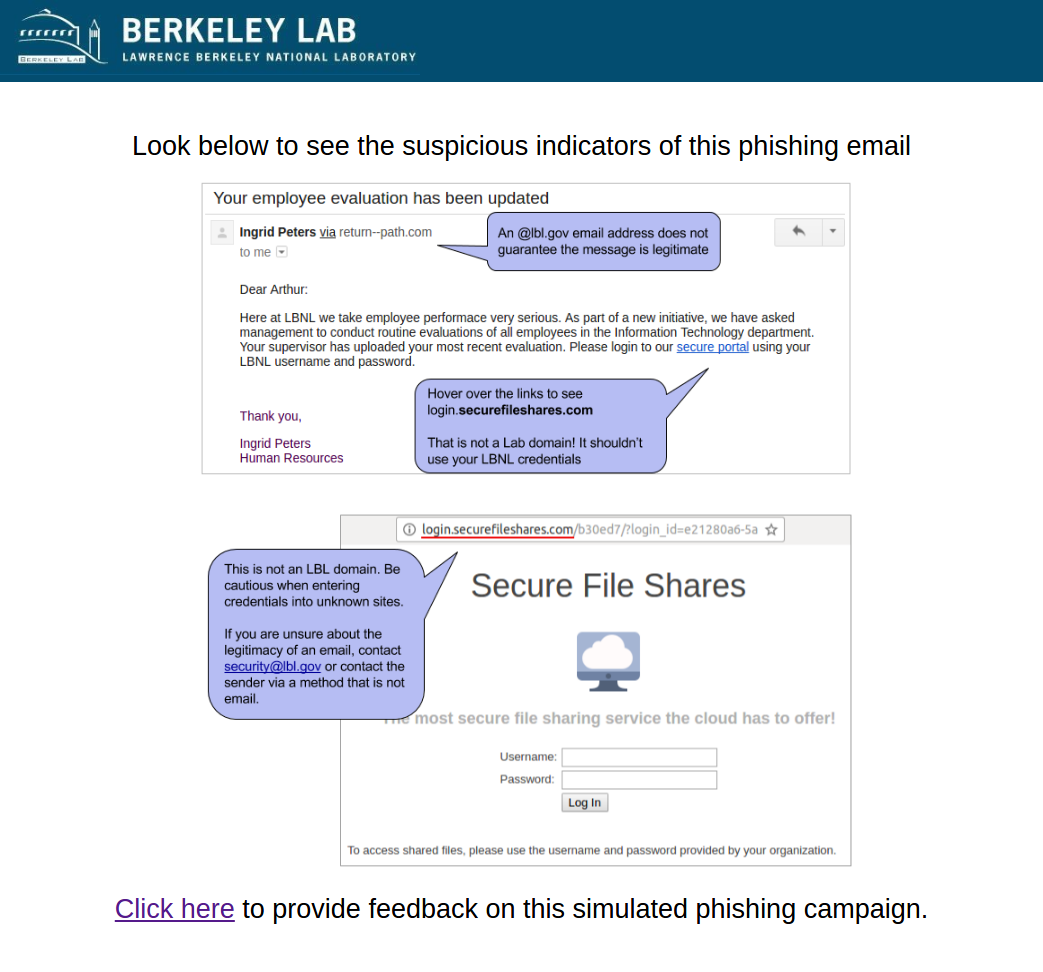
#4 2017-03-14: Employee evaluation
This email was intended to get users to question the request to input credentials into a non-LBL site. The link in the email directed to a non-LBL login page in order to tempt users to enter passwords. The fake employee Ingrid Peters was reused from the previous phish. Ingrid was added to the user directory to demonstrate the situation where an email address is spoofed or compromised. A phone number was added to Ingrid's directory entry that would be answered by security group.
...
The Landing Page:
The Education Page:
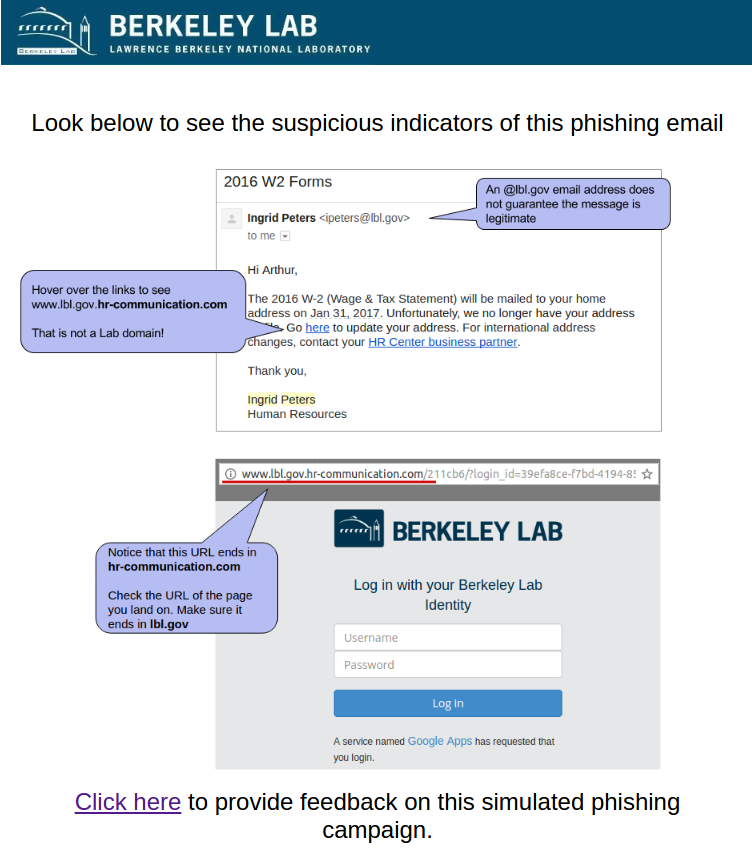
#3 2017-01-18: 2016 W2 Forms - lost mailing address
This email was intended to get users to focus on the URL despite the use of a "real" lbl.gov email address. The link in the email directed to a fake LBL login page in order to tempt users to enter passwords. The fake employee Ingrid Peters was added to the user directory to demonstrate the situation where an email address is spoofed or compromised. A phone number was added to Ingrid's directory entry that would be answered by security group.
...
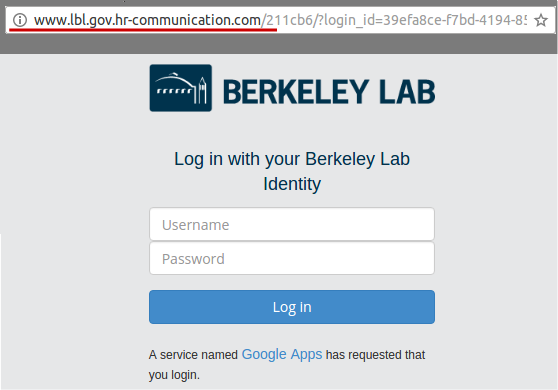
The Landing Page:
The Education Page:
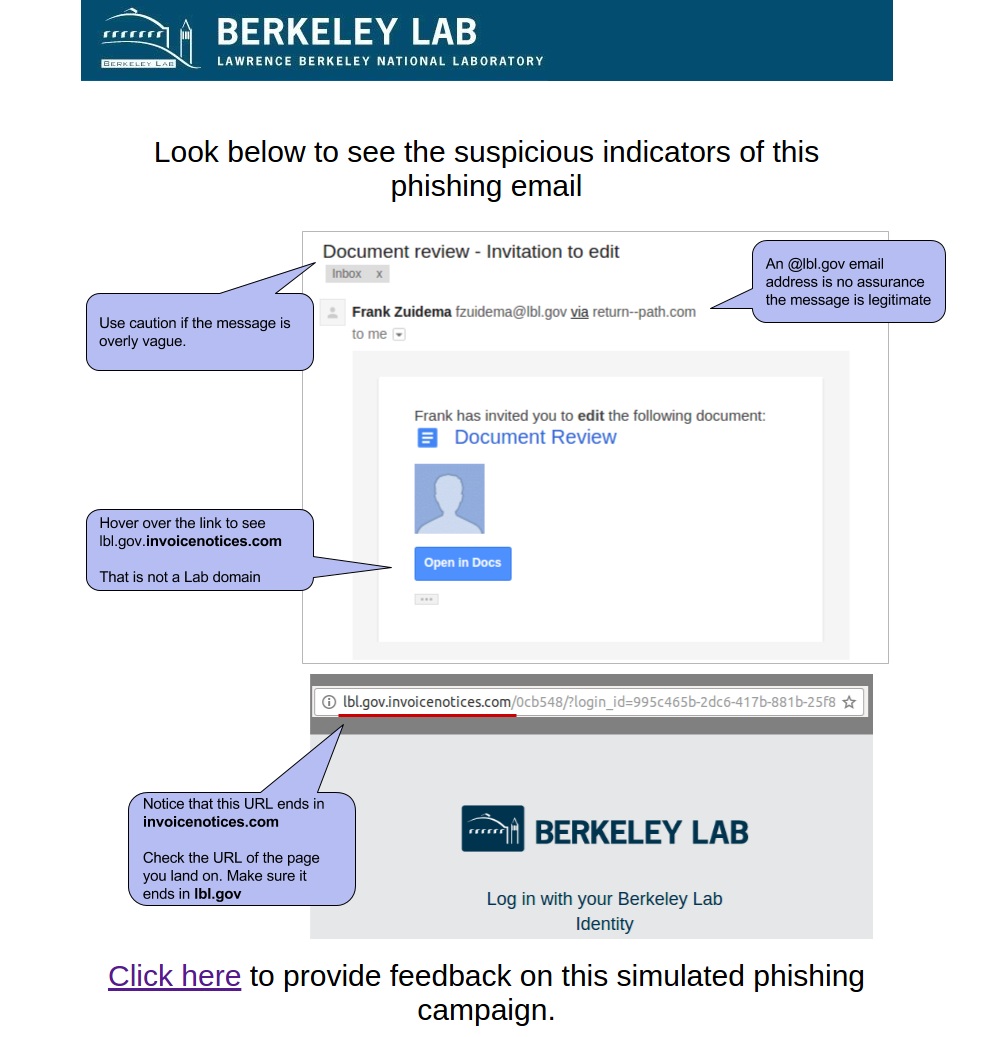
#2 2016-12-06: Google Document Invitation to edit
This email was intended to get users to focus on the URL and demonstrate that it is often trivial to make a email or web site that looks like ones you trust. It mimicked the HTML of a real "Invitation to Edit" email sent by Google Drive as well as the LBL login page. The email appeared to be from an LBL employee (although this user doesn't exist).
...
The Landing Page:
The Education Page:
#1 2016-10-08: Urgent - Email Reactivation
This email was our first phish and intended to test the waters. It emulated the common phishing emails that are vague, urgent, and not necessarily relevant. It had an fake sender address that appeared to be from within LBNL.
...