An undulator is a periodic structure of magnets through which an electron bunch goes radiating synchrotron light towards the forward direction. It has been widely used at synchrotron light facilities, such as the Advanced Light Source (ALS, US), European Synchrotron Radiation Facility (ESRF, EU), etc. In spectrum calculation, the sampled trajectories of electrons in a bunch are traced through the measured magnetic field given by a table, then the associated radiation is calculated for each trajectory and integrated at a given observation point downstream of the undulator structure. The spectrum calculation of undulator radiation is becoming more and more compute intensive primarily due to the dramatic increase in the sample number of electrons in a bunch.
Today, HPC Services staffer Yong Qin will be presenting his work during a poster session at this week's GPU Technology Conference, GTC 2013, in San Jose, California. Yong's work demonstrates how data parallelism can be applied to spectrum calculation of undulator radiation, which is widely used at synchrotron light facilities across the world. This poster presents the algorithm design and performance optimization details for NVIDIA Fermi GPUs. Performance data from multiple optimization efforts and algorithms will be compared. Advanced topics, such as multiple GPUs, hybrid computing will also be demonstrated on how to further improve the field performance. An overall more than 400 of parallel speedup is achieved on one Fermi C2050 GPU with 448 cores, with close to linear scalability.
The climate models that scientists use to understand and project climate change are improving constantly, with better representations of the oceans, ice, land surfaces and other factors in the atmosphere. While there is still some degree of uncertainty in all these components, the largest source of uncertainty in today’s climate models are clouds.
Clouds can both cool the planet, by acting as a shield against the sun, and warm the planet, by trapping heat. But why do clouds behave the way they do? And how will a warming planet affect the cloud cover?
Lawrence Berkeley National Laboratory scientist David Romps has made it his mission to answer these questions. His work involves the development of cloud resolution models on a dedicated 336-core Dell cluster and the Lab's Lawrencium cluster - both managed by the IT Division's High Performances Services Group. More...
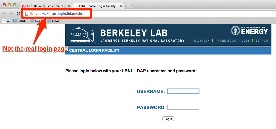
Suspicious feeling leads IT’s Susan Green to report targeted attack
Maybe it comes from working for 15 years in Berkeley Lab’s IT Division, but administrative assistant Susan Green likes to keep a close eye on her email, even those messages that end up in her spam folder. On Jan. 25, she saw a message announcing an update to Berkeley Lab Gmail and opened the message. Inside, the text looked legitimate, but the return address caught her attention.
“Although it read like a normal memo, it didn’t seem quite right – it didn’t have an lbl.gov address,” Green said. “I noticed the word ‘lawyer’ in the email address, which wasn’t right.”
Instead of clicking on the link in the message – and since the message mentioned Gmail – Green took it to another IT employee, who was on a conference call. Green showed it to another IT manager, but was worried that she might be making a big deal out of nothing. But then the IT manager asked her to forward the message and they found a sophisticated attack targeting specific Lab employees.
“They took the legitimate Lab logon page, duplicated it exactly, and rehosted it on another server,” said Jay Krous of the Computer Protection Program. “We saw that they took the time to craft it specifically for LBNL folks – it wasn’t like the usual bank scams with misspelled words. In fact, they used the same words as are on our website. That’s when we went into alarm mode.”
The Computer Protection Program team immediately blocked access to the server from the lab, then went to work finding out who received the message. In all, 363 employees were targeted. And what they all have in common is that they buy airline tickets and make travel arrangements.
Apparently the people behind the attack hoped to obtain the employee credentials and purchase tickets on small foreign airlines – airlines that allow purchasers to return unused tickets for cash.
It turns out the targeted phishing attack had been tried in the exact same way against a number of other .edu sites. Another sign of the attack’s sophistication is that the subject line varied and the messages came from two different addresses, making it harder to block.
“People reporting these malicious email are an important part of our protection strategy. Thanks to Susan following her intuition, we were able to block this early, and no one at the lab logged into the fake site,” Krous said. “It’s important that employees alert us as soon as they see something that doesn’t seem right – the sooner we hear about it, the sooner we can block it.”
Krous said employees should report malicious emails targeting their UC, DOE, or Berkeley Lab affiliations to [email protected]. And, of course, use caution with messages or attachments that are from people you don’t know or that you aren’t expecting.
For more cyber security information, visit the Berkeley Lab Computer Protection Program web site. For more information and examples of targeted phishing you can go here.
We plan to take our enterprise directory service down at 10pm, Saturday March 9 for a 30 minute maintenance period. This will impact all authentications to lab systems including cloud based services like Google. For many, this service is commonly known as "LDAP". It will also impact access to the new One-time-Password (OTP) Service that is being gradually phased in by IT staff.
One of our goals is to re-implement an approach to Password Expiration - Lab employees who have not changed their password within the past several months will be put on a staggered schedule (with appropriate notifications) - during April and May. Passwords will be set to expire on workdays when the IT Help Desk can assist if needed (Tuesdays through Thursdays) if notifications have not been acted upon.
This will not impact Mobile phone access to Google mail or calendar.
For the past couple of years, Manymoon - an early Google Marketplace tool - has been available through the "More" Menu when logged into any of the core Google Applications.
We never found a great business need for this tool. Now that the company has been acquired by Salesforce and the product converted to "DO", we feel the time has come to remove it from our portfolio of applications. Individual users can still use the free version by going directly to the companies website, according to Manymoon support staff, but as of Friday March 8, it will no longer be part of our environment.